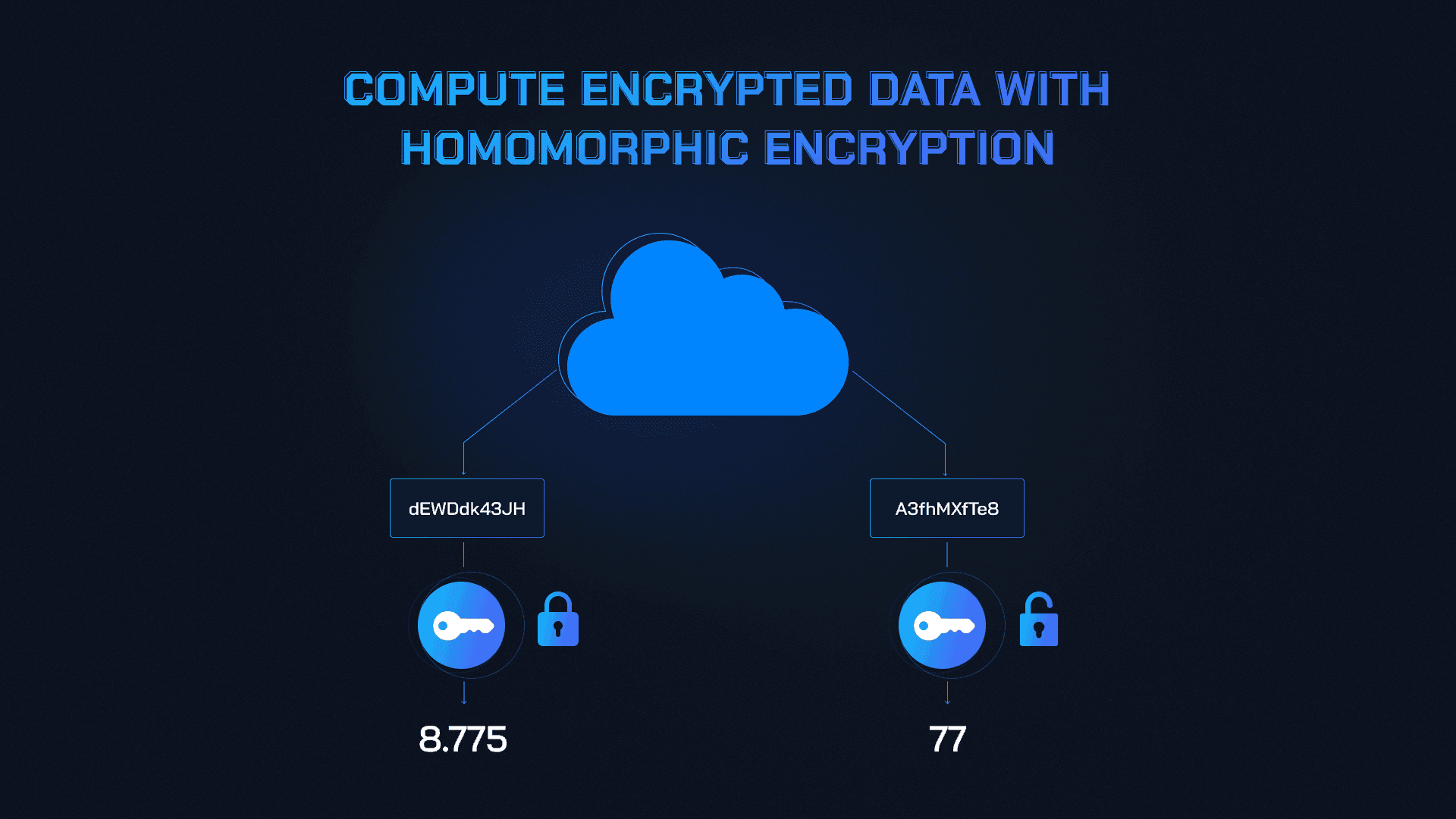
In the evolving landscape of blockchain, where transparency clashes with the imperative of privacy, decentralized confidential compute networks stand as a beacon of secure innovation. Drawing from my two decades modeling bond yields under strict confidentiality, I see Fully Homomorphic Encryption (FHE) libraries not merely as tools, but as foundational pillars for bootstrapping these networks. They enable computations on encrypted data without decryption, preserving sensitivity in Web3 environments. FHEToolkit. com equips developers with precisely such libraries, optimized for private onchain compute.
Recent advancements underscore this shift. dFHE's distributed infrastructure accelerates FHE by 100x via a hybrid Residue Number System, transforming encrypted data processing efficiency. Fhenix introduces a coprocessor for off-chain services compatible with Ethereum, allowing smart contracts to handle end-to-end encrypted data. Arcium, evolving from Elusiv, leverages MPC, FHE, and ZKP on Solana for parallel confidential computing. These developments, alongside OpenFHE's open-source implementations succeeding PALISADE, signal a maturing ecosystem for FHE confidential compute networks.
Why FHE Libraries Outpace Traditional Privacy Tech
Trusted Execution Environments like SGX, explored by Flashbots, and multi-party computation offer privacy, yet falter under decentralization's scrutiny. FHE sidesteps these pitfalls by natively supporting arithmetic on ciphertexts, ideal for decentralized FHE toolkits. Oasis Protocol redefines developer toolsets, while Secret Network's EVM-focused primitives enable privacy-preserving AI. NVIDIA's CUDA enhancements hint at hardware convergence, but true decentralization demands software like OpenFHE, blending schemes from HElib and beyond.
Reflecting conservatively, FHE's mathematical rigor appeals over speculative TEEs. In finance, where macro cycles demand unseen bond yield models, FHEToolkit. com's libraries mirror this: secure, scalable, and blockchain-agnostic. Projects like 180Protocol's modular kits and Atoma Network's Web3 AI platform build atop such foundations, fostering private blockchain interoperability.
Key FHE Libraries
- OpenFHE: Open-source cross-platform library implementing FHE schemes, succeeding PALISADE with features from HElib and others.
- dFHE: Distributed infrastructure accelerating FHE by 100x via hybrid Residue Number System architecture.
- Fhenix CoFHE: FHE coprocessor enabling off-chain encrypted computations compatible with EVM chains.
- Arcium: DePIN network for parallel confidential computing on Solana, integrating FHE with MPC and ZKP.

Laying the Groundwork with Open-Source FHE
OpenFHE emerges as the linchpin, incorporating HEAAN and FHEW for versatile schemes. Developers bootstrap networks by integrating these into Solidity via Hardhat or Remix, as Messari notes in privacy layer analyses. Cocoon's open network for ML and Solidus AI's Secret Network partnership exemplify deployment: privacy-preserving models without exposing inputs.
Yet bootstrapping demands deliberation. Unlike centralized clouds, DeCC networks require resilient, verifiable compute. Chainlink Confidential Compute's framework adds end-to-end verifiability, a reflective nod to institutional needs. At FHEToolkit. com, our tutorials guide from scheme selection to onchain deployment, emphasizing low-risk fundamentals over hype.
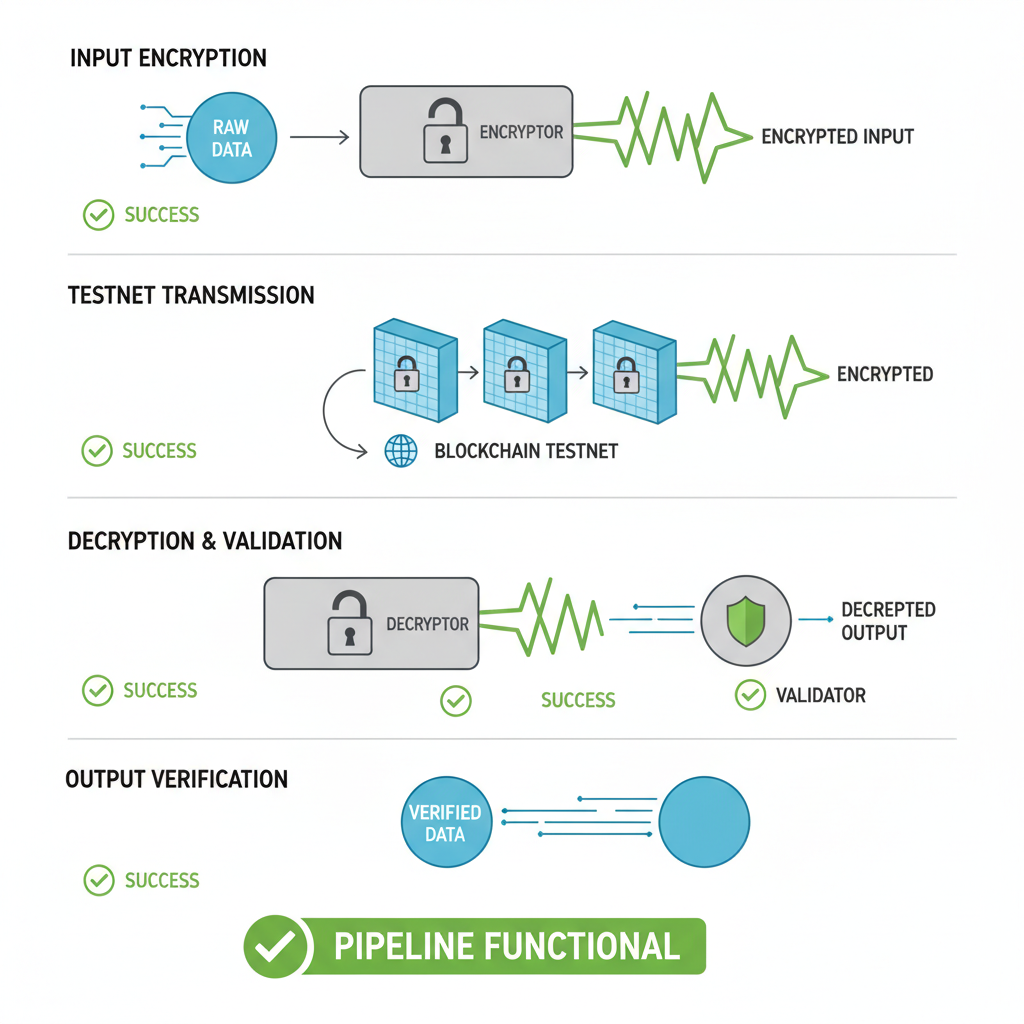
Core Steps to Bootstrap Your DeCC Network
Initiating a network mirrors fixed income portfolio construction: methodical, privacy-first. Select FHE schemes suited to workload, integrate via libraries, and orchestrate nodes for distributed evaluation. This reflective process yields robust FHE bootstrap guides, scalable across ecosystems.








No comments yet. Be the first to share your thoughts!